How Community Banks Turn Regulatory Updates into Structured Gap Analysis in Minutes, Not Days
An AI agent reads the bulletin, maps it against your policy inventory, and delivers a severity-rated action plan with deadlines. You review it.
Four Updates, Three Days, One Analyst
Monday morning at a $600 million community credit union with 45,000 members. The compliance officer opens her regulatory feed and finds four new items: an OCC bulletin on third-party risk management with a July effective date, a CFPB advisory opinion on overdraft fee disclosures, an NCUA supervisory letter on cybersecurity expectations for federally insured credit unions, and a FinCEN advisory on emerging BSA/AML risks in peer-to-peer payment services. Each one has a different effective date. Each one touches different parts of the institution's policy inventory. The FinCEN advisory's effective date is ten days out.
She has one compliance analyst. A shared-drive policy inventory with seven core policies covering vendor management, information security, BSA/AML, business continuity, board reporting, data protection, and training. A three-business-day SLA the board expects for impact assessments. And an OCC exam scheduled for September.
She starts with the OCC bulletin because the July effective date feels close. She opens the vendor management policy in one browser tab and the bulletin in another. The bulletin requires a centralized vendor inventory with risk ratings updated at least annually. Her current policy calls for annual review of critical vendors and biennial review for non-critical vendors. That is a gap. She writes it down. The bulletin also requires formal escalation procedures for vendor non-compliance with SLA or security requirements. She searches through the policy. No escalation procedures documented. Another gap. The bulletin further requires concentration risk assessment for vendors providing similar services. Not addressed anywhere in the current policy. Three gaps from one bulletin, and she has only finished comparing it against one of the four policies it affects.
The bulletin also impacts board reporting (no specific third-party risk reporting in the quarterly board presentation), and business continuity (critical vendor dependencies identified, but no formal vendor failure contingency plans). That is three more policies to pull up, read through provision by provision, and compare against the new requirements. She assigns each gap a severity: critical, because the effective date is July and policy changes take time to draft, approve, and implement. She estimates deadlines: policy amendments need to be done by June 1 to leave 30 days of buffer before the effective date.
Four to six hours later, she has a thorough analysis of one bulletin. Three more are waiting.
62% of compliance officers spend one to seven hours weekly just tracking regulatory developments, according to Thomson Reuters. That is before they start the actual analysis. At community institutions receiving five to fifteen regulatory updates per month that require action, the math breaks. A two-person compliance team cannot give each update a thorough, policy-by-policy analysis within the SLA window and still prepare for exams, update training materials, and report to the board. Something gets abbreviated. Some updates get a skim and a note that says "reviewed, no action needed" when a careful reading would have found a gap in the data protection policy or a missing provision in the training program.
The institution does not know what it missed until the examiner asks.
Why the Usual Fixes Break Down at the Analysis Step
The compliance officer's problem is not a lack of information about regulatory changes. It is a lack of time to analyze what those changes mean for her specific policy inventory.
Regulatory intelligence services like Compliance Alliance or Banker's Toolbox solve the notification problem well. They curate alerts, provide plain-language summaries, and tell you what changed. But they stop at notification. The compliance officer still has to open her vendor management policy, read through its provisions, compare them against the specific requirements in the OCC bulletin, identify that "biennial review for non-critical vendors" does not satisfy "annual risk ratings for all vendors," and document that gap with a severity rating and a deadline. The intelligence service told her the bulletin exists. It did not tell her that three provisions in her vendor management policy, two in her business continuity plan, and one in her board reporting framework are insufficient.
Enterprise GRC platforms like MetricStream or ServiceNow GRC promise to centralize this work. They do, for institutions that can afford them. Implementation timelines run six to twelve months. Configuration requires mapping the institution's entire control framework into the platform's taxonomy. Annual licensing exceeds what many community bank compliance budgets can support. And even after adoption, 77% of compliance teams still rely on manual processes for regulatory change management, according to CUBE's 2025 Cost of Compliance Report. The platform becomes a place to record the analysis. It does not do the analysis.
The spreadsheet tracker is where most compliance teams live. Columns for regulatory source, effective date, applicability, policy owner, status. It works at low volume. But a spreadsheet has no version control on the analysis itself, no structured mapping to specific policy provisions, and no audit trail that satisfies an examiner asking "show me how you determined this update did not require changes to your information security policy." When the examiner opens the spreadsheet and sees "Reviewed, N/A" next to an NCUA supervisory letter that clearly required MFA for privileged accounts, the conversation gets uncomfortable fast.
The core difficulty is this: comparing regulatory language against policy provisions is not keyword matching. The OCC bulletin says "risk ratings updated at least annually." The vendor management policy says "annual review for critical vendors" and "biennial review for non-critical vendors." A keyword search finds "annual" in both documents and marks them as aligned. A compliance officer reads the bulletin and recognizes that "all vendors" is broader than "critical vendors" and that the biennial cycle for non-critical vendors creates a gap. That judgment — understanding scope, comparing thresholds, recognizing when a provision partially addresses a requirement but not fully — is where the manual hours live. No notification service or spreadsheet performs it.
lasa.ai built an AI agent that maps regulatory requirements against your policy inventory and generates a structured gap analysis with severity ratings and deadlines.
See what this looks like for your compliance process →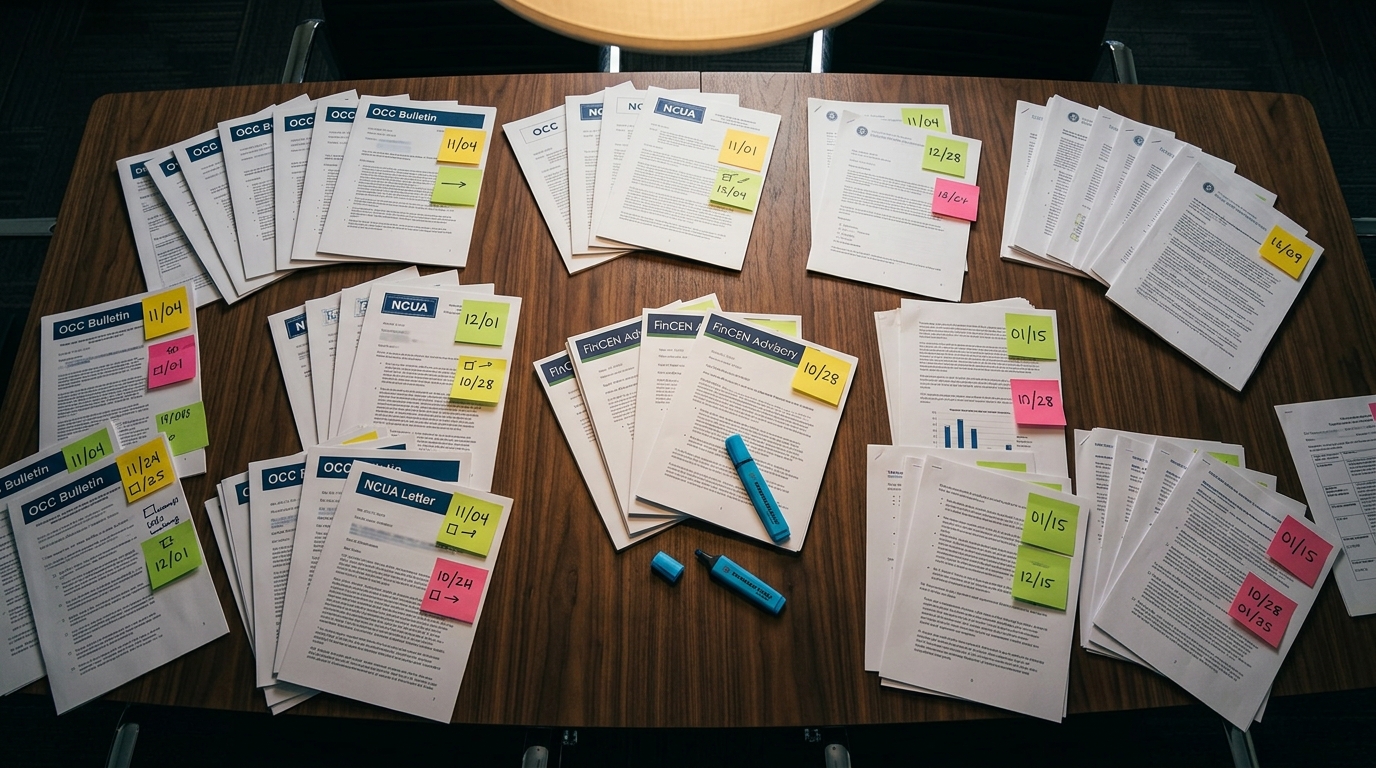
From Reading Bulletins to Reviewing Assessments
The shift is not from manual to automated. It is from reading to reviewing.
Instead of opening each regulatory update and each policy side by side, the compliance officer gives the AI agent two things: the regulatory updates (the OCC bulletin, the NCUA supervisory letter, the FinCEN advisory) and the institution's policy inventory. The agent reads both. It maps the specific requirements in each update against the specific provisions in each affected policy. It identifies where the current policy language does not meet the new requirement, or where a requirement addresses something the institution has no policy for at all. It assigns severity based on the gap type and the regulation's effective date. It generates an action plan with deadlines, owners, and the specific policy amendments needed.
The compliance officer's job becomes reviewing the assessment, not producing it. She reads the gap analysis table, confirms or adjusts the severity ratings, adds institutional context the agent does not have (a board meeting is scheduled for May, so the vendor management policy amendment should be on that agenda), and sends the report to the compliance committee. The expertise is still hers. The hours of side-by-side reading are not.
This matters most for the updates that would otherwise get abbreviated. The FinCEN advisory on P2P payment risks? That one touches the BSA/AML policy in four distinct ways: transaction monitoring lacks P2P-specific detection scenarios, enhanced due diligence procedures do not trigger on P2P volume, SAR investigative checklists do not include P2P typologies, and no documented P2P risk assessment exists. A quick skim might catch one or two of those. The agent catches all four because it compares every requirement against every provision. Thoroughness is not aspirational. It is structural.
What the Impact Assessment Actually Contains
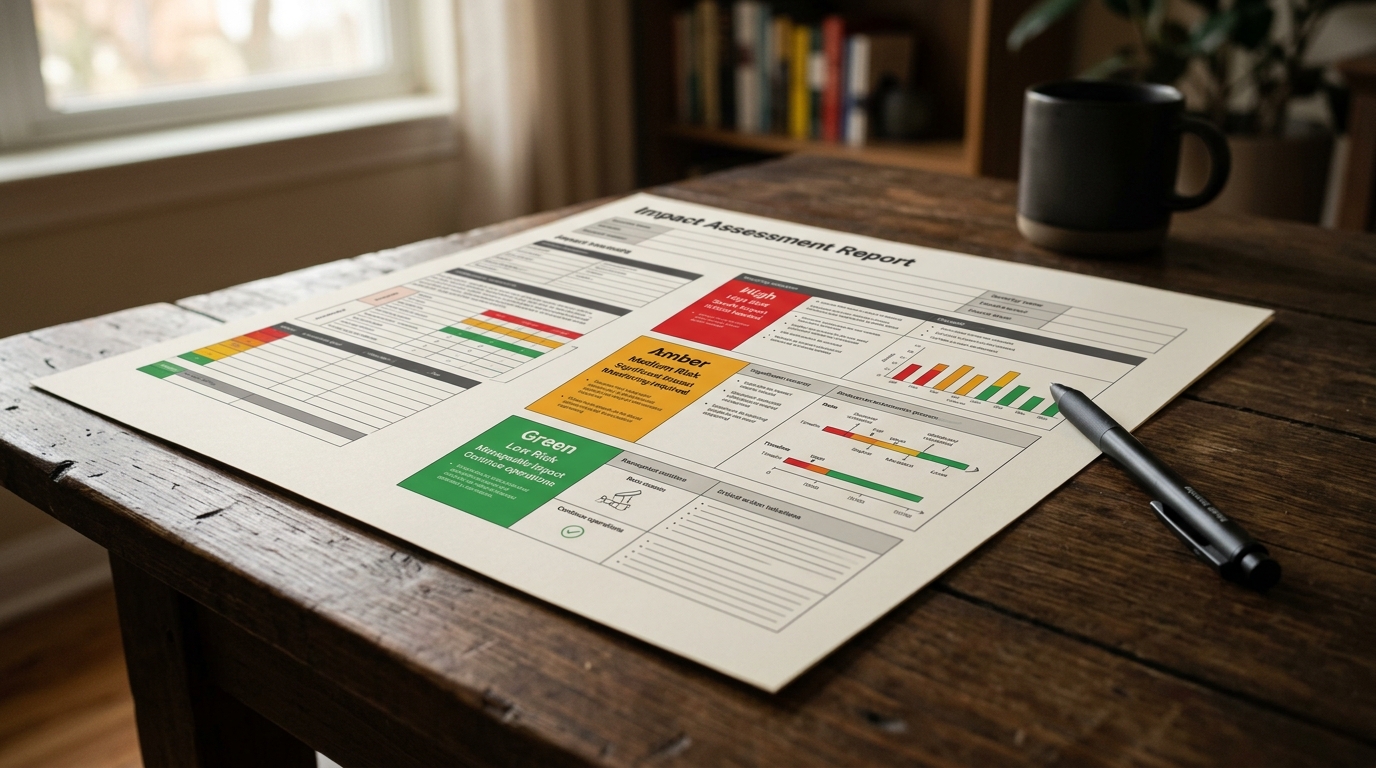
Walk through a concrete example. The AI agent receives an OCC bulletin on third-party risk management with a July 1 effective date and compares it against the institution's policy inventory.
The agent identifies three affected policies. For the vendor management policy, it finds three gaps. First: the policy requires annual review for critical vendors and biennial review for non-critical vendors, but the bulletin requires annual risk rating updates for all vendors. Gap: biennial review cycle for non-critical vendors does not meet the annual requirement. Severity: critical. Action required: amend the policy to mandate annual risk ratings for all vendors. Second: no formal escalation procedures for vendor non-compliance are documented anywhere in the current policy. The bulletin explicitly requires them. Severity: critical. Third: no concentration risk framework exists. Severity: critical.
For the business continuity plan, the agent identifies that critical vendor dependencies are documented and recovery time objectives exist, but no formal contingency plans address the scenario of a critical vendor failing entirely. The bulletin requires it. Severity: critical. Deadline: June 1, thirty days before the July effective date.
For board reporting, the current quarterly presentation covers general compliance status but includes no specific third-party risk section. The bulletin requires quarterly reporting on third-party risk status to the board or a designated committee. Severity: critical.
The output is a structured document. It opens with an executive summary: three regulatory updates analyzed, seven policies reviewed, fourteen required actions identified (eight critical, five high, one moderate). Board-ready. That summary is what the compliance committee chair reads before deciding which items go on the May board agenda.
Below the summary, each update gets its own section with a gap analysis table. Five columns: Policy, Current State, Gap Identified, Severity, Action Required. Not a narrative essay about the bulletin. A table the compliance officer can scan in minutes and mark up with her own notes.
Then the consolidated action plan. Every action item across all updates, sorted by deadline. The FinCEN items with the April 10 effective date appear first, flagged as past due if the assessment runs after that date. The OCC items with June 1 deadlines come next. The NCUA cybersecurity items with September 1 deadlines follow. Each line includes the regulation reference, the affected policy, the severity, the deadline, and the assigned owner.
Finally, a 90-day deadline calendar. Not every item on the calendar, just the ones with dates in the next quarter. The compliance officer prints this and tapes it to the wall next to her monitor. It is the ugliest part of the report and the most useful.
What Changes When Every Update Gets a Thorough Analysis
Before: a compliance officer spends four to six hours per regulatory update doing the manual comparison work. With ten updates in the queue and competing priorities, some get abbreviated review. The compliance committee receives a summary reflecting what the officer had time to analyze, not what actually changed. When the examiner asks about a specific bulletin, the officer produces a Word document or spreadsheet entry that may or may not demonstrate a thorough analysis. The smallest banks spend 11 to 15.5% of their total payroll on compliance, compared to 6 to 10% at the largest institutions. Most of that disparity is not regulation volume. It is the manual labor that does not scale down.
After: each update gets the same thorough treatment. The four-to-six-hour manual analysis becomes thirty to forty-five minutes of review. Not because corners were cut, but because the reading-and-mapping work was done before the compliance officer opened the report. She spends her time on the parts that require her judgment: adjusting severity ratings based on institutional context, sequencing action items around the board calendar and exam schedule, and deciding which items to escalate to the compliance committee immediately versus including in the next quarterly review.
The examiner asks about the March OCC bulletin. The compliance officer produces a structured impact assessment showing every requirement in the bulletin mapped against every affected policy, with gaps documented, severity assigned, and actions tracked. Not a spreadsheet row that says "Reviewed." A provision-by-provision analysis. That is a different conversation.
The compliance analyst who used to spend her week pulling up policies and bulletins side by side now spends her time on implementation: drafting policy amendments, updating training materials, preparing the board presentation. The upstream work shifted from production to quality control.
Healthcare compliance teams mapping CMS final rules against patient safety protocols face the same structural problem. So do insurance carriers tracking state insurance department requirements across thirty jurisdictions. The regulatory body changes. The effective dates change. The pattern (map incoming requirements against an existing policy inventory, identify gaps, prioritize by deadline) does not. The same structured analysis approach that works for an OCC bulletin on third-party risk also works for SAR narrative drafting, where transaction alerts must be mapped against regulatory reporting requirements and institutional thresholds before a narrative is produced.
Huh. The same problem everywhere. Different acronyms.
Regulatory change impact analysis is one pattern. lasa.ai runs it for compliance teams across banking, healthcare, and insurance, anywhere a regulated entity needs to map evolving requirements against existing policies before enforcement.
See what this looks like for your institution →The regulatory burden on a community bank is not the complexity of any single bulletin. It is the compound effect of five to fifteen updates per month, each requiring provision-level comparison against multiple policies, with overlapping effective dates and a two-person team that also has an exam to prepare for.
Frequently Asked Questions
How do community banks track regulatory changes?
What is regulatory change management in banking?
How long does it take to implement a regulatory change?
What happens if a bank fails to comply with a new regulation?
See What This Looks Like for Your Process
Let's discuss how LasaAI can automate this for your team.